Content Security Policy: The Bodyguard Your Site Needs
By The bee2.io Engineering Team at bee2.io LLC
Your website is basically walking around with its fly open and nobody has the heart to tell you.
Not literally, obviously. But metaphorically? Your scripts are hanging out, your third-party integrations are doing whatever they want, and hackers are actively looking for ways to inject malicious code into your users' browsers. This is where Content Security Policy (CSP) enters the chat like a massive, invisible bodyguard who says "no" to sketchy stuff.
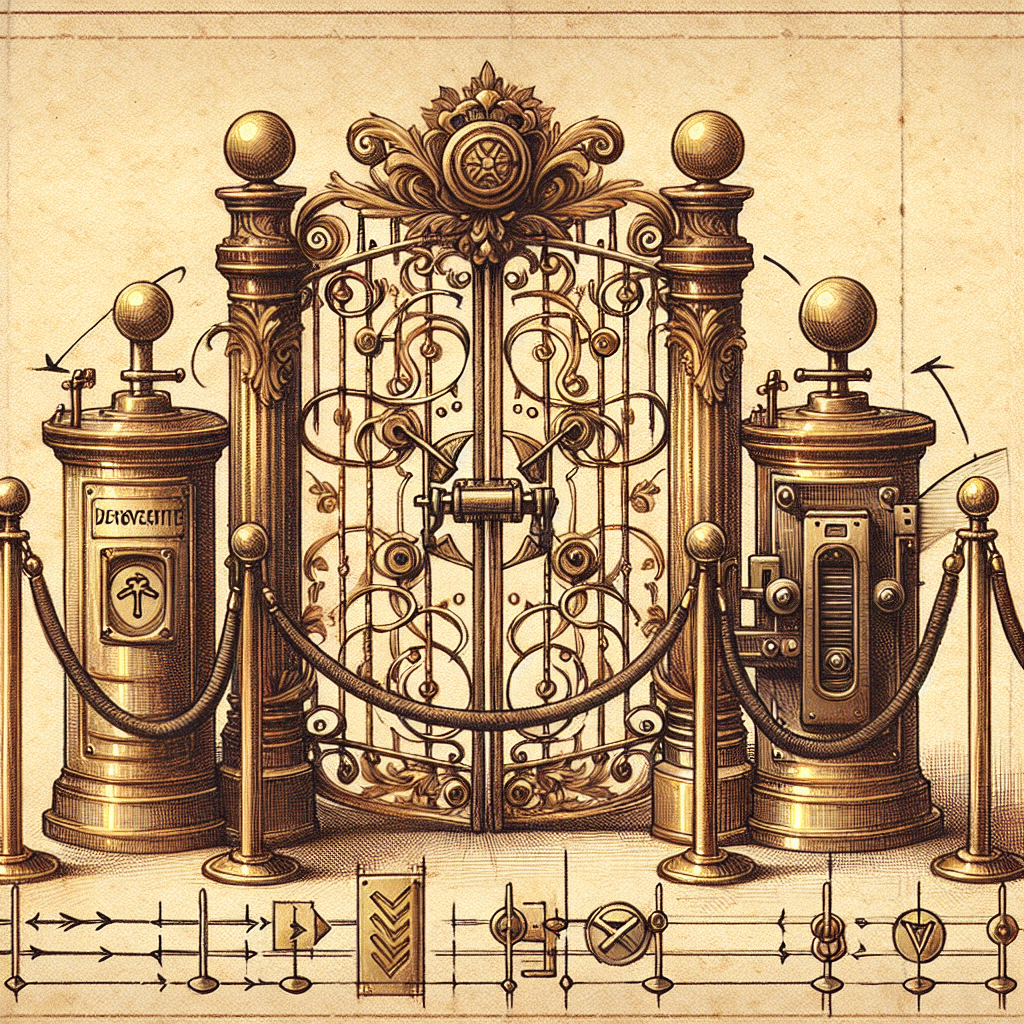
Think of CSP as the bouncer at an exclusive club, except the club is your website and the VIP list is called a whitelist. Without it, literally anyone can walk in and tell your visitors their password is expired. With it? Only the people you specifically invited get through the velvet rope.
What's XSS and Why Should You Care?
Cross-Site Scripting (XSS) is when an attacker injects malicious JavaScript into your website. Your users load the page thinking everything's normal, but surprise - they're actually running code that steals their credentials, redirects them to a phishing site, or silently harvests their data. It's the web development equivalent of someone handing you a coffee that tastes fine but is actually poison.
Here's the terrifying part: industry data suggests that XSS vulnerabilities account for roughly 15% of all web application attacks. That's one in six attacks we're talking about. And the worst part? Many sites still aren't protecting themselves because "implementing security feels hard" (it doesn't, we'll prove it).
CSP prevents this by telling the browser: "Hey, only load scripts from these exact sources. Everything else? Blocked. No exceptions. No negotiation." It's like issuing your browser a laminated list of trusted friends and saying "only listen to them."
The Directives: Your New Best Friends
CSP works through directives - think of them as specific security rules for different types of content. You don't need to memorize all of them (that's what documentation is for, duh), but here are the heavy hitters:
script-src
This is the main event. It controls which sources can execute JavaScript on your page.
- 'self' - Only scripts from your own domain. Revolutionary, we know.
- 'none' - No inline scripts at all. Extreme? Yes. Effective? Also yes.
- Specific URLs - Trust Google Analytics but not that sketchy ad network? List the exact domains.
- 'unsafe-inline' - This basically means "ignore everything we just said and let scripts run everywhere." Don't do this. Seriously. We're begging you.
style-src
Same concept but for CSS. Because attackers can also inject malicious styles (yes, really - they can exfiltrate data through CSS). The fact that this is possible makes us all question our life choices.
img-src, font-src, connect-src
These control images, fonts, and API connections respectively. You probably don't need to lock these down as tight as scripts, but options exist. You're welcome.
Here's a basic example that's actually useful:
Content-Security-Policy: script-src 'self' https://cdn.example.com; style-src 'self' https://fonts.googleapis.com; img-src 'self' https:; connect-src 'self' https://api.example.com;
Translation: Trust only our own scripts and one CDN. Trust our styles and Google Fonts for CSS. Load images from anywhere secure. And only let API calls go to our own domain and our backend. That's not insane, that's intelligent.
Deployment: From Theory to "Oh Crap, It Actually Works"
You can deploy CSP two ways:
- As an HTTP header - The server sends the policy with every response. This is the nuclear option and what you should eventually do.
- As a meta tag - Stick it in your HTML head for quick testing. Not production-ready, but great for "let's see if this breaks everything."
Pro tip that will save you hours of debugging: start with Content-Security-Policy-Report-Only. This lets CSP report violations without actually blocking anything. It's like running a fire drill before there's a fire - infinitely less stressful than discovering a broken integration at 2 AM because you blocked the wrong script source.
Most frameworks (we won't name names, but they rhyme with "Ext.js" and "Sails") have middleware that makes CSP implementation laughably easy. If your framework doesn't, congratulations, you've discovered why that framework is getting sunset.
The Bottom Line
CSP isn't perfect - no security measure is - but it's genuinely one of the highest return-on-investment security controls you can implement. It stops a huge category of attacks dead in their tracks with relatively minimal effort.
Your users are trusting you with their data. The least you can do is make sure only your code is running on their browsers, not some random attacker's.
Want to know if your site has proper CSP set up? Use SCOUTb2's browser extension to scan your domain and get a real picture of what you're dealing with. Spoiler alert: it probably shows something interesting.
Disclaimer: This article is for informational purposes only and does not constitute legal, professional, or compliance advice. SCOUTb2 is an automated scanning tool that helps identify common issues but does not guarantee full compliance with any standard or regulation.
Stop finding issues manually
SCOUTb2 scans your entire site for accessibility, performance, and SEO problems automatically.