The HTTPS Padlock Is Lying to You
By The bee2.io Engineering Team at bee2.io LLC
Every web browser shows it. That little padlock icon next to the URL. Millions of people see it and think: "Great, this site is secure. I can now safely enter my credit card number, my mother's maiden name, and possibly my childhood pet's social security number." And they are wrong. Not completely wrong. But wrong enough that it matters a lot.
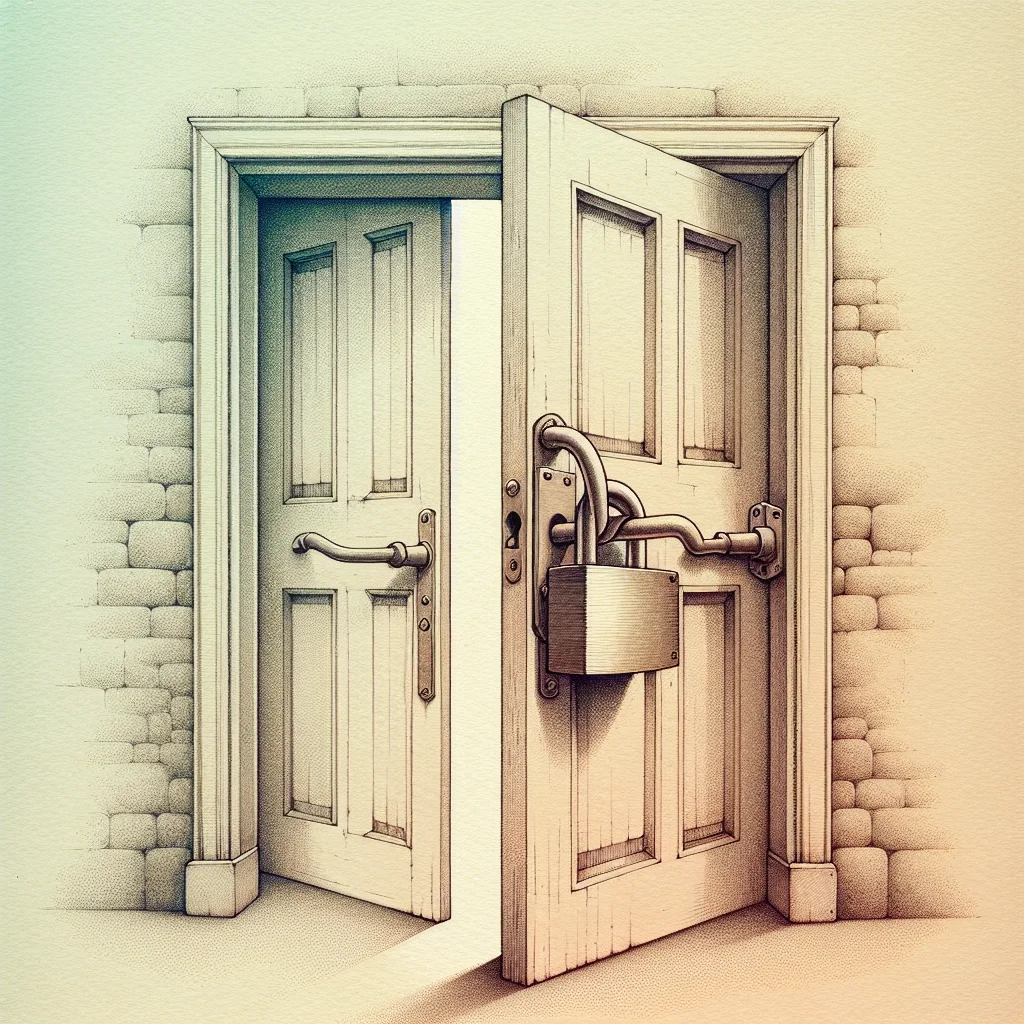
The padlock means one thing and one thing only: the connection between your browser and the server is encrypted. It does not mean the website is trustworthy. It does not mean your data is handled responsibly. It does not mean the site is free from vulnerabilities. It just means nobody can eavesdrop on the data in transit. This is the web dev equivalent of putting a padlock on your front door while leaving every window open, the back door unlocked, and a helpful sign in the yard reading "KEY IS UNDER THE MAT."
A phishing site can have a padlock. A site riddled with cross-site scripting vulnerabilities can have a padlock. A site that stores your password in a text file named "passwords_lol.txt" can have a padlock. The padlock is a transport security indicator, not a quality seal.
The Security Layers Nobody Sees (Because They Are Doing Their Jobs)
HTTPS is the floor, not the ceiling. It is the minimum viable security configuration. Bragging about having HTTPS in 2026 is like bragging about wearing pants to a job interview. Technically correct, but the bar is higher than that. The real protection comes from the layers on top of it:
- HSTS (Strict-Transport-Security): Forces the browser to always use HTTPS, closing the brief vulnerability window during the first connection. Without it, a user typing "yoursite.com" gets a brief HTTP connection before redirecting to HTTPS, and that brief moment is exploitable. It is a very small window, but hackers are very patient people with very small tools.
- Content-Security-Policy: Controls exactly which scripts and resources can load on your page. This is the primary defense against cross-site scripting (XSS) attacks. Without it, your site is basically an improv theater where any script can walk on stage and start performing.
- Mixed content prevention: Loading even one image or script over HTTP on an HTTPS page creates a security hole. It is like building an armored vault and then installing a cat flap.
- Secure cookie flags: Cookies without the Secure flag can be transmitted over unencrypted connections. Cookies without HttpOnly can be stolen by malicious scripts. It is the digital equivalent of writing your passwords on a sticky note and then leaving it on the bus.
The Mixed Content Trap (You Probably Fell Into It)
Here is a scenario that happens more often than anyone admits: you set up HTTPS, got the padlock, and celebrated. Maybe you even posted about it. But your CSS file loads a font from an HTTP URL. Or your blog post embeds an image from an HTTP source. Or a third-party widget injects an HTTP script like an uninvited guest bringing their uninvited friend.
That is mixed content. And it is surprisingly common. One study found that roughly 30% of HTTPS sites still load at least one resource over plain HTTP. The browser might still show the padlock, but the security guarantee has a hole in it big enough to drive a truck through.
Beyond the Padlock (Where the Real Security Lives)
The next time you see that padlock, remember what it actually means: the connection is encrypted. Nothing more, nothing less. The real security of a website is determined by its headers, its content policy, its cookie configuration, and a dozen other factors that are invisible to the naked eye. It is like judging a restaurant by the door handle instead of the kitchen.
A quick security scan can reveal all of these invisible layers. It takes seconds, and the results are often eye-opening. You might be surprised how many gaps exist behind that reassuring little padlock. It is less "Fort Knox" and more "pillow fort" for most sites.
Disclaimer: This article is for informational purposes only and does not constitute legal, professional, or compliance advice. SCOUTb2 is an automated scanning tool that helps identify common issues but does not guarantee full compliance with any standard or regulation.
Stop finding issues manually
SCOUTb2 scans your entire site for accessibility, performance, and SEO problems automatically.