Your Website Has a Secret Guest List (And Bots Love It)
By The bee2.io Engineering Team at bee2.io LLC
Your website is basically hosting an open-bar house party where the front door has been removed from its hinges, the snack table is unguarded, and someone has written "FREE STUFF, COME ON IN" on the sidewalk in neon paint. Bots, scrapers, clickjackers, and automated vulnerability scanners are showing up in droves. They did not even bring a bottle of wine. Rude.
The difference between a secure site and an all-you-can-eat buffet for malicious actors often comes down to a handful of HTTP response headers that take about five minutes to configure. Five minutes. That is less time than you spend deciding what to have for lunch.
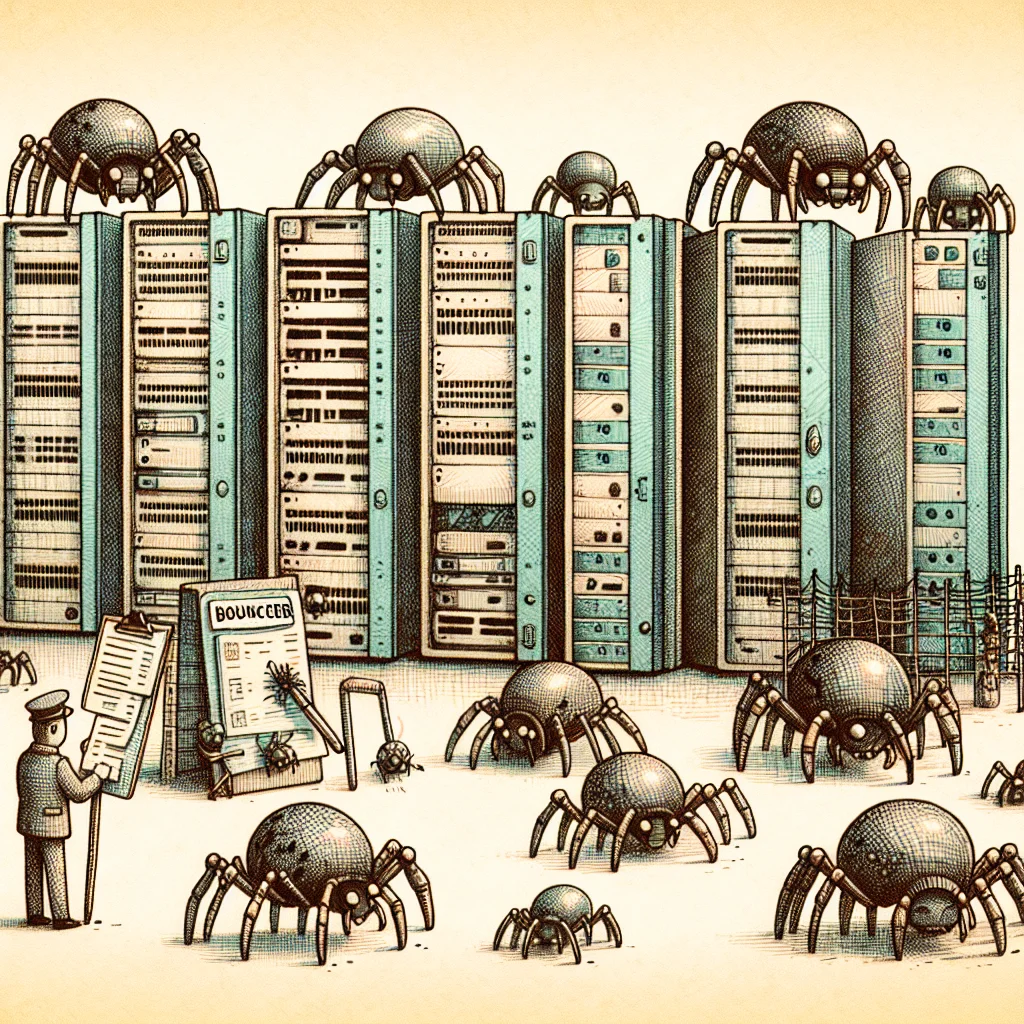
The Bouncer You Forgot to Hire (He Is Still Waiting by the Phone)
HTTP security headers are instructions your server sends to the browser before the page even loads. Think of them as the rules posted at the entrance of a nightclub. Except your nightclub currently has no rules, no bouncer, and the DJ is playing "Welcome Hackers" on repeat.
Here are the big ones you need to care about:
- Content-Security-Policy (CSP) tells the browser exactly which scripts, styles, and resources are allowed to load. Without it, any injected script can waltz in and do whatever it wants. It is like telling your bouncer "only people on this list get in" versus telling him "sure, let that guy with the crowbar in, he seems nice."
- Strict-Transport-Security (HSTS) forces browsers to use HTTPS, even if someone types HTTP. Without it, there is a brief window where traffic can be intercepted. It is the difference between a sealed envelope and shouting your credit card number across a crowded food court.
- X-Frame-Options prevents your site from being embedded in an iframe on someone else's page. This stops clickjacking attacks, where an attacker overlays invisible buttons on top of your site. Imagine someone taping a fake "donate to charity" button over your real "transfer $5,000" button. Charming.
- X-Content-Type-Options prevents browsers from guessing the type of a file. Sounds harmless, until a browser decides your innocent text file is actually an executable script and runs it like an eager intern who was told to "just handle it."
The Five-Minute Check That Prevents the Five-Month Nightmare
The uncomfortable truth: checking your security headers takes less time than making a cup of coffee. And I mean instant coffee, not the fancy pour-over thing. Open your browser DevTools, go to the Network tab, click on your homepage request, and look at the response headers. If you do not see Content-Security-Policy, Strict-Transport-Security, or X-Frame-Options, your website is essentially standing on the internet corner with a sign that reads "HACK ME, I DARE YOU."
A quick automated scan can check all of this in seconds and tell you exactly which headers are missing, misconfigured, or redundant. No security degree required. No monocle either.
Why This Should Bother You More Than It Currently Does
According to published web security research, over 70% of websites are missing at least one critical security header. Seventy percent. That is like finding out 70% of houses in your neighborhood leave the front door unlocked. These are not exotic configurations. They are basic hygiene, like washing your hands before making someone a sandwich. You would not skip that. Please tell me you would not skip that.
The real cost of ignoring security headers is not a dramatic Hollywood-style hack with green text scrolling down a screen. It is the slow, silent erosion of trust. A customer gets phished through a clickjacked page. A search engine flags your site. A compliance audit fails. These things compound like bad Yelp reviews.
Stop Reading and Go Fix This
Run a quick scan on your site. If your security headers section looks emptier than a gym in February, add the basics: CSP, HSTS, X-Frame-Options, X-Content-Type-Options, and Referrer-Policy. Most can be added in a single configuration line. The before-and-after difference in your scan results will be dramatic, like those home renovation shows but for your server.
Your website's guest list should be intentional, not accidental. The bots will still show up. But at least now they will have to knock instead of walking in with their shoes on your white carpet.
Disclaimer: This article is for informational purposes only and does not constitute legal, professional, or compliance advice. SCOUTb2 is an automated scanning tool that helps identify common issues but does not guarantee full compliance with any standard or regulation.
Stop finding issues manually
SCOUTb2 scans your entire site for accessibility, performance, and SEO problems automatically.